HIPAA for Dummies
What HIPAA Means
Our HIPAA for Dummies guide starts by explaining what HIPAA means because many people associate the Health Insurance Portability and Accountability Act solely with the Administrative Simplification provisions and the Privacy, Security, and Breach Notification Rules that evolved as a result of HIPAA.
Additionally, it is not only important to understand what HIPAA means, but also why HIPAA was created, what its purpose was, and how the Administrative Simplification provisions – which include the Privacy, Security, and Breach Notification Rules – evolved from the original Act of legislation.
Why was HIPAA Created?
Prior to the passage of HIPAA, the health insurance industry was regulated by a mixture of state and federal laws. Most commercial group health plans were governed by state laws, while most employer-sponsored and individually purchased health plans were subject to the Employee Retirement Income Security Act of 1974 (ERISA) and the Consolidated Omnibus Budget Reconciliation Act of 1985 (COBRA).
This created a scenario in which employees risked losing health insurance benefits if they changed jobs – or risked being denied insurance in a new job if they had developed a medical condition in their previous job which was excluded from coverage. This “job lock” scenario not only affected employees, but also made it difficult was some employers to attract skilled workforces – especially in evolving industries such as the technology industry.
HIPAA was created to resolve this issue by increasing the portability of health insurance between jobs and prohibiting practices that denied or limited access to health care benefits – such as increased premiums for employees with pre-existing conditions. In addition, rather than applying to employer-sponsored and individually purchased health plans, HIPAA applied to all health insurance plans, no matter what type of health plan it was.
What is the Purpose of HIPAA?
Although the purpose of HIPAA was to reform the health insurance industry, the objectives of increased portability and accountability would have cost the insurance industry a lot of money – which would have been recovered from group plan members and employers as higher premiums and reduced benefits. To address this issue, Congress added further measures to HIPAA to reduce fraud and abuse and improve efficiency by simplifying the administration of health claims.
At the time, fraud and abuse in the healthcare industry accounted for around 10% of total healthcare spending – some of which was due to different organizations using different codes for the same healthcare transactions. By bringing in tougher penalties for fraud and abuse, and by instructing the Secretary of Health and Human Services (HHS) to standardize transaction code sets, Congress was able to reduce fraud and create a mechanism for better policing healthcare transactions.
As an increasing volume of patient medical and payment information was being transmitted electronically, HHS was also instructed to develop standards to ensure the confidentiality, integrity, and availability of electronically-transmitted health data, and – at the end of the Administrative Simplification provisions – to draw up a list of recommendations “with respect to the privacy of certain health information”. These recommendations later became the HIPAA Privacy Rule.
What HIPAA Does Not Cover
 There are quite a lot of things that HIPAA does not cover, and it is probably easier to summarize what HIPAA covers – particularly with regards to the privacy of health information and the confidentiality, integrity, and availability of electronically-transmitted health data. Possibly the most important consideration in this context is who HIPAA applies to because there are examples of individuals and businesses unnecessarily withholding information believing it was covered by HIPAA.
There are quite a lot of things that HIPAA does not cover, and it is probably easier to summarize what HIPAA covers – particularly with regards to the privacy of health information and the confidentiality, integrity, and availability of electronically-transmitted health data. Possibly the most important consideration in this context is who HIPAA applies to because there are examples of individuals and businesses unnecessarily withholding information believing it was covered by HIPAA.
HIPAA applies to health plans, healthcare clearing houses and healthcare providers that transmit information electronically in connection with a transaction for which HHS has published standards. However, there are exceptions. Insurance companies that pay for medical care or equipment secondary to a primary insurance (i.e., auto insurance) are not covered by HIPAA. Also, healthcare professionals such as counsellors and therapists are also not covered by HIPAA if they only bill patients directly.
Financial institutions that process payments on behalf of health plans and healthcare providers are not covered by HIPAA – even though the transaction may disclose patient medical and payment information. Additionally, school medical centers are not covered by HIPAA because students´ health records are considered to be part of their educational records under FERPA. However, exceptions to this exception exists if the medical center also provides treatments for members of the public.
Understanding HIPAA for Dummies
One of the most misunderstood concepts in HIPAA is what is Protected Health Information. This is because, although the definition of Personal Health Information in the Administrative Simplification provisions is clear (i.e., any individually identifiable health information relating to an individuals health, health care, or payment for health care), a number of sources include individually identifiable non-health information in their definitions.
This is likely attributable to non-health information being subject to the same privacy and security standards as health information when it is maintained in the same designated record set as health information. The reason for the misunderstanding about what is Protected Health Information is because the Privacy Rule lists eighteen personal identifiers that must be removed from a designated record set before the set can be considered de-identified and no longer subject to HIPAA standards.
| Names or part of names | Any other unique identifying characteristic |
| Geographical identifiers | Dates directly related to a person |
| Phone number details | Fax number details |
| Details of Email addresses | Social Security details |
| Medical record numbers | Health insurance beneficiary numbers |
| Account details | Certificate or license numbers |
| Vehicle license plate details | Device identifiers and serial numbers |
| Website URLs | IP address details |
| Fingerprints, retinal and voice prints | Complete face or any comparable photographic images |
It is important to be aware that, if non-health information is maintained in a separate database that does not contained health information, it is not PHI nor protected by the Privacy Rule standards (although other state privacy laws may apply). Additionally, the list of eighteen personal identifiers does not include potential identifiers that have emerged since the publication of the Privacy Rule – for example, social media aliases and details of emotional support animals.
The main takeaway for HIPAA compliance is that any company or individual subject to HIPAA that comes into contact with PHI must enact and enforce appropriate policies, procedures and safeguards to protect data. HIPAA violations occur when there has been a failure to enact and enforce appropriate policies, procedures and safeguards, even when PHI has not been disclosed to or accessed by an unauthorized individual.
Violations of HIPAA often result from the following:
- Lack of adequate risk analyses.
- Lack of comprehensive employee training.
- Inadequate Business Associate Agreements.
- Inappropriate disclosures of PHI.
- Ignorance of the minimum necessary rule.
- Failure to report breaches within the prescribed timeframe.
Some HIPAA violations are accidental offences – for example, leaving a document containing PHI on a desk in clear view of anyone passing by. However, HHS’ Office for Civil Rights (OCR) does not consider ignorance an adequate excuse for HIPAA violations; and, although OCR may refrain from imposing a significant financial penalty on a Covered Entity for an accidental offence if the violation has not resulted in the unauthorized disclosure of unsecure PHI, it may be likely that a course of “corrective action” is required.
HIPAA Rules Explained
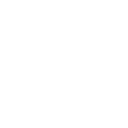
HIPAA legislation is essentially comprised of a number of rules, each of which lays out different requirements for HIPAA compliance. The rules are as follows:
HIPAA Privacy Rule: The Privacy Rule dictates how, when, and under what circumstances PHI can be used and disclosed. It also includes standards giving patients´ rights over their health information and more control over how it is used and disclosed.
The Privacy Rule sets limits regarding the use of patient information when no prior authorization has been given by the patient. Additionally, it mandates patients and their representatives have the right to obtain a copy of their health records and request corrections to errors.
HIPAA Security Rule: The Security Rule sets standards to protect ePHI. All Covered Entities and third party Business Associates that perform a service for or on behalf of a Covered Entity must comply with all the Security Rule standards.
There are five parts of the Security Rule – the General Rules (which covers the “flexibility of approach” standard relating to how all the other standards should be implemented, the Administrative, Physical, and Technical Safeguards, and the Organization Requirements – which cover relationships between Covered Entities and Business Associates.
Breach Notification Rule: The Department of Health and Human Services must be notified if a data breach has been discovered. This must be within 60 days of the breach’s discovery for incidents involving 500 or more individuals, and within 60 days of the end of the calendar year in which the breach was experienced for breaches of fewer than 500 records.
Individuals whose personal information has been compromised must also be informed within 60 days, and if more than five hundred individuals are affected in a particular jurisdiction, a media notice must be issued to a prominent news outlet serving that area.
Omnibus Rule: The Omnibus Rule activated most HIPAA-related changes that had been part of the HITECH Act. These included the extension of HIPAA coverage to BAs, the prohibition of using PHI for marketing or fundraising purposes without authorization, and new penalty tiers for violations of HIPAA.
Enforcement Rule: Should a violation of HIPAA occur, this Rule lays out how any resulting investigations are carried out. In most cases, Covered Entity or Business Associate agree to “voluntary compliance” sometimes supported by technical assistance from OCR. However, OCR has the authority to impose civil monetary penalties and corrective action plans on non-compliant Covered Entities and Business Associates. Since 2009, State Attorneys General have also had the authority to pursue civil monetary penalties when a HIPAA violation results in a data breach.
An exception to the enforcement process can occur if a Covered Entity, Business Associate, or a member of either’s workforce is suspected to have knowingly and wrongfully disclosed PHI (or caused PHI to be disclosed) in violation of §1177 of the Social Security Act. In such circumstances, the OCR investigation is referred to the Department of Justice to pursue a criminal conviction. If found guilty, the penalty for knowingly and wrongfully disclosing PHI is a fine of up to $250,000 and up to ten years in jail.
The Required and Addressable Security Measures of HIPAA Explained
The HIPAA Security Rule list the conditions (“safeguards”) that must be in place for HIPAA-compliant storage and the communication of ePHI. These “safeguards” are referred to in the HIPAA Security Rule as either “required” or “addressable”. In fact, all the security measures are generally required – irrespective of how they are listed – as the following explains:
One area of HIPAA that has resulted in some confusion is the difference between “required” and “addressable” security measures. Practically every safeguard of HIPAA is “required” unless there is a justifiable rationale not to implement the safeguard, or an appropriate alternative to the safeguard is put in place that achieves the same objective and provides an equivalent level of protection.
An instance in which the implementation of an addressable safeguard might be not required is the encryption of email. Emails containing ePHI – either in the body or as an attachment – only have to be encrypted if they are shared beyond a firewalled, internal server. If a healthcare group only uses email as an internal form of communication – or has an authorization from a patient to send their information unencrypted outside the protection of the firewall – there is no need to adopt this addressable safeguard.
The decision not to use email encryption will have to be backed up by a risk assessment and must be documented in writing. Other factors that may have to be considered are the organization’s risk mitigation strategy and other security measures put in place to secure the integrity of PHI. As a footnote to this particular section of our HIPAA for Dummies guide, the encryption of PHI at rest and in transit is recommended.
HIPAA Encryption Requirements
HIPAA-covered entities are required to implement safeguards to ensure the confidentiality, integrity, and availability of ePHI. Arguably one of the most important safeguards is encryption, especially on portable devices such as laptop computers that are frequently taken off site.
 Encryption renders ePHI unreadable and undecipherable. The data can only be read if a key or code is applied to decrypt the data. If a portable device containing encrypted ePHI is stolen, and the code or key to decrypt the data is not also obtained, the data cannot be viewed.
Encryption renders ePHI unreadable and undecipherable. The data can only be read if a key or code is applied to decrypt the data. If a portable device containing encrypted ePHI is stolen, and the code or key to decrypt the data is not also obtained, the data cannot be viewed.
While HIPAA was deliberately technology-agnostic, data encryption is mentioned in the HIPAA Security Rule, but it is only an addressable specification. HIPAA-covered entities must consider using encryption, but it is not mandatory for ePHI to be encrypted at rest or in transit.
HIPAA-covered entities should conduct a risk analysis and determine which safeguards are the most appropriate given the level of risk and their workflow.
If the decision is taken not to use encryption, an alternative safeguard can be used in its place, provided it is reasonable and appropriate and provides an equivalent level of protection. If encryption is not used, the decision not to encrypt must be documented along with the reasons why encryption was not used and the alternative safeguards that were used in its place.
If the decision is taken to encrypt data, HIPAA-Covered Entities should use an appropriate encryption standard. The National Institute of Standards and Technology (NIST) recommends Advanced Encryption Standard (AES) 128, 192 or 256-bit encryption, OpenPGP, and S/MIME – although these standards may change.
HIPAA Password Requirements
HIPAA is “flexible” when it comes to specific technologies and controls that should be applied to secure ePHI and systems that store health information, and this is certainly true for passwords.
 Even though passwords are one of the most basic safeguards to prevent unauthorized access to data and accounts, there is little mention of passwords in HIPAA. The only HIPAA password requirements that are specified are that HIPAA-covered entities and their business associates must implement “Procedures for creating, changing, and safeguarding passwords.”
Even though passwords are one of the most basic safeguards to prevent unauthorized access to data and accounts, there is little mention of passwords in HIPAA. The only HIPAA password requirements that are specified are that HIPAA-covered entities and their business associates must implement “Procedures for creating, changing, and safeguarding passwords.”
Even though password requirements are not detailed in HIPAA, HIPAA covered entities should develop policies covering the creation of passwords and base those policies on current best practices. It is strongly recommended that healthcare organizations follow the advice of NIST when creating password policies.
While NIST has previously recommended the use of complex passwords, its advice on passwords has recently been revised. Highly complex passwords may be ‘more secure’ but they are difficult to remember. As a result, employees often write their passwords down. To avoid this, passwords should be difficult to guess but also memorable. The use of long passphrases rather than passwords is now recommended.
Generally, passwords should:
- Be a minimum of 8 characters up to 64 characters, with passphrases – memorized secrets – longer than standard passwords recommended.
- NIST advises against storing password hints as these could be accessed by unauthorized individuals and be used to guess passwords.
- A password policy should be implemented to prevent commonly used weak passwords from being set, such as ‘password’, ‘12345678’, ‘letmein’ etc.
- NIST now recommends not forcing users to change their passwords frequently. A change should only be required infrequently or is there is very good reason for doing so – such as following a security breach.
- Multi-factor authentication should be implemented.
- NIST recommends salting and hashing stored passwords using a one-way key derivation function.
For a full list of password best practices, readers are advised to review NIST SP 800-63B
HIPAA Record Retention Requirements
There are no HIPAA record retention requirements as far as medical records are concerned. Medical record retention requirements are covered by state laws, and data retention policies for medical records must be developed accordingly.
For instance, a hospital in the state of South Carolina must retain medical records for 11 years after the discharge date, while in Florida medical records must be retained by physicians for five years after the last patient contact and hospitals must retain medical records for seven years after the discharge date.
 When medical records are retained, they must be kept secure at all times. HIPAA requires appropriate administrative, technical, and physical safeguards to be implemented to ensure the confidentiality, integrity, and availability of ePHI from the date of creation of ePHI to its secure disposal.
When medical records are retained, they must be kept secure at all times. HIPAA requires appropriate administrative, technical, and physical safeguards to be implemented to ensure the confidentiality, integrity, and availability of ePHI from the date of creation of ePHI to its secure disposal.
While there is not a HIPAA medical record retention period, HIPAA does require covered entities to retain HIPAA-related documents. CFR §164.316(b)(2)(i) states that HIPAA-related documents must be retained for a period of six years from the date that the document was created. For policies, it is six years from when the policy was last in effect.
Insurance companies may be subject to FINRA laws which cover the retention of certain records. The Fair Labor Standards Act and the Employee Retirement Income Security Act also require certain records to be retained and the Centers for Medicare & Medicaid Services (CMS) requires healthcare providers to retain cost reports for five years after the closure of the cost report, while Medicare managed care program providers are required to retain records for ten years.
HIPAA Violation Reporting Requirements
The HIPAA Breach Notification Rule – 45 CFR §§ 164.400-414 – requires notifications to be issued after a breach of unsecured protected health information.
A breach is defined as a use or disclosure of protected health information not permitted by the HIPAA Privacy Rule that compromises the security or privacy of protected health information. Notifications are not required if a HIPAA-covered entity or business associate can demonstrate there is a low probability that PHI has been compromised, with that determination made through a risk analysis.
If notifications are required, they must be issued to patients/health plan members ‘without unnecessary delay’ and no later than 60 days after the discovery of a breach. A media notice must also be issued if the breach impacts more than 500 individuals, again within 60 days. The notice should be provided to a prominent media outlet in the state or jurisdiction where the breach victims are located.
The individual and media notices should include a brief description of the security breach, the types of information exposed, a brief description of what is being done by the breached entity to mitigate harm and prevent future breaches, and the steps that can be taken by breach victims to reduce the potential for harm.
HHS’ Office for Civil Rights must also be notified within 60 days of the discovery of a breach if the breach impacts 500 or more individuals, and within 60 days of the end of the calendar year in which the breach was experienced if the breach impacts fewer than 500 individuals.
A copy of the breach notices should be retained along with documentation showing that notifications were issued. If a security breach did not warrant the issuing of notifications, documentation must be retained detailing the risk assessment that established there was a low probability that PHI was compromised.
Most Common HIPAA Violations
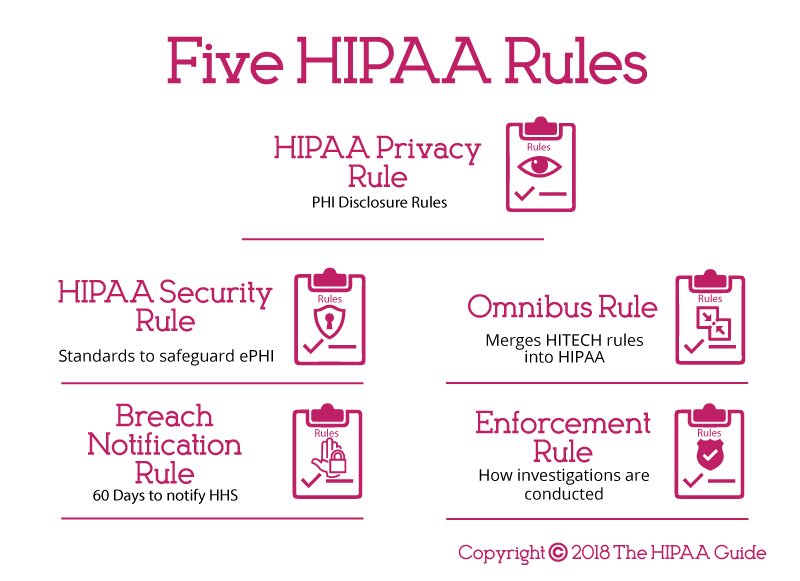
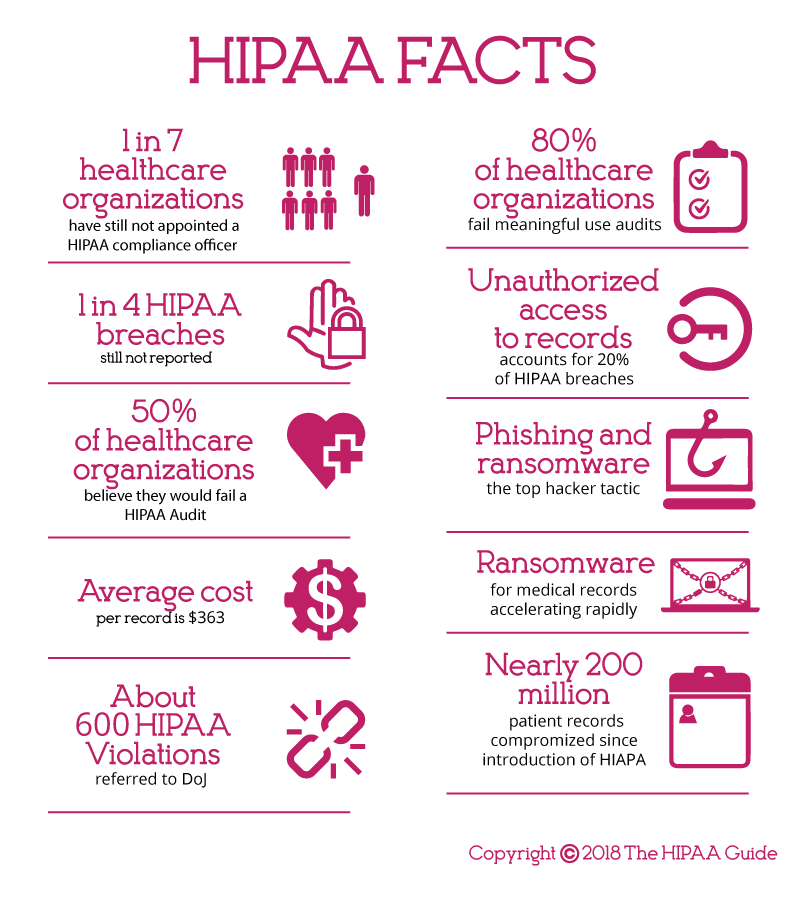
A HIPAA violation is the failure to comply with any applicable provisions of the HIPAA Rules. While there are many potential areas where HIPAA Rules can be violated, ten of the most common HIPAA violations are detailed below. These violations have been discovered by OCR during investigations of data breaches and complaints filed by workforce members, patients, and plan members through the OCR complaints portal.
Risk Analysis Failures
One of the most common HIPAA violations discovered by OCR is the failure to perform a comprehensive, organization-wide risk analysis. HIPAA requires covered entities and their business associates to conduct regular risk analyses to identify vulnerabilities to the confidentiality, integrity, and availability of PHI.
Risk Management Failures
All risks identified during the risk analysis must be subjected to a HIPAA-compliant risk management process and reduced to a reasonable and appropriate level. Risk management is critical to the security of ePHI and PHI and is a fundamental requirement of the HIPAA Security Rule.
Lack of Encryption or Alternative Safeguards
While HIPAA does not demand the use of encryption, encryption is an addressable implementation specification and must be considered. The failure to use encryption or an alternative equivalent safeguard to ensure the confidentiality, integrity, and availability of ePHI has resulted in many healthcare data breaches.
Security Awareness Training Failures
HIPAA requires covered entities and business associates to implement a security awareness training program for all members of the workforce, including management. HIPAA training should be provided regularly and the frequency should be determined by means of a risk analysis.
Improper Disposal of PHI
When PHI or ePHI is no longer required it must be disposed of securely in a manner that ensures PHI is “unreadable, indecipherable, and otherwise cannot be reconstructed.” Paper records should be shredded, burnt, pulped, or pulverized, while electronic media should be cleared, purged, degaussed, or destroyed.
Impermissible Disclosures of PHI
An impermissible disclosure of PHI is a disclosure not permitted under the HIPAA Privacy Rule. This includes providing PHI to a third party without first obtaining consent from a patient and ‘disclosures’ when unencrypted portable electronic devices containing ePHI are stolen.
Failure to Adhere to the Minimum Necessary Standard
Covered entities must take steps to limit access to PHI to the minimum necessary information to achieve the intended purpose.
Failure to Provide Patients with Copies of PHI on Request
The Privacy Rule permits patients to access PHI and obtain copies of their protected health information on request. Requests for copies of PHI must be dealt with promptly and copies provided within 30 days of the request being received.
Failure to Enter into A Business Associate Agreement
Covered Entities may require third parties to provide services that require access to PHI. Prior to any disclosure of PHI, the entity that provides the services for or on behalf of the Covered Entity must enter into a business associate agreement (BAA) with the covered entity. The BAA outlines the business associate’s responsibilities to safeguard PHI, explains the permissible uses and disclosures of PHI, and other requirements of HIPAA.
Failure to Issue Breach Notifications Promptly
In the event of a data breach, notifications must be issued to affected individuals to alert them to the exposure of their PHI. Breach notifications must be issued without unreasonable delay and no later than 60 days from the date of discovery of the breach.
HIPAA Implications for Patients
The HIPAA implications for patients are that their healthcare information is treated more sensitively and can be accessed more quickly by their healthcare providers. Electronically stored health information is now better secured than paper records ever were, and healthcare groups that have put in place mechanisms to adhere with HIPAA regulations are witnessing greater efficiency. This results – as far as patients are concerned – in a higher standard of healthcare.
On the negative side, healthcare groups are not only concerned with the standard of healthcare they can give to individual patients. Healthcare groups want to increase the services they can provide, want to enhance the quality of care, and improve patient safety through research. Regrettably, research is limited by HIPAA, and restricted access to PHI has the potential to slow the pace at which improvements can be made in healthcare.
There is also a price to pay for better data security, and although the enactment of the Meaningful Use program gave financial incentives for healthcare providers to digitalize paper records, adapting the necessary controls to secure ePHI can carry a substantial cost. Increasing funding for compliance may reduce the level of patient care, while the administrative strain that HIPAA-compliance places of healthcare organizations furthers exhausts available resources.
Explaining HIPAA to Patients
Healthcare organizations are required by law to give patients a notice of their privacy practices and get patients to sign to confirm receipt of the document. It is also necessary to post the Notice of Privacy Practices in a prominent position in a physical service delivery site and on a web page. Because there is often a great deal of information that needs to be included in a Notice, it is not reasonable to expect a patient to absorb all the information during the first encounter. Because of this, it is a good practice to put key information in a handout and refer the patient to the Notice of Privacy Practices for more information. For example, a handout could include information such as:
- They may request their medical records whenever they like.
- They may request you amend their medical records to correct errors.
- They can limit who has access to their personal health information.
- They can choose how you communicate with them.
- They have right to complain about the unauthorized disclosure of their PHI and suspected HIPAA violations.
It is also important that any member of the workforce that interacts with patients is fully aware of the procedures when a patient exercises their right to request a copy of their medical records or restrict disclosures of PHI. The failure to respond to a patient’s request in a timely manner can result in a complaint being files with HHS’ Office for Civil Rights and a compliance investigation. For the avoidance of doubt, all references to members of the workforce in this HIPAA for Dummies guide includes employees, students, volunteers, and clergy under the control of a covered entity or business associate regardless of whether they are paid by the covered entity or business associate.
Healthcare Organizations and the Implications of HIPAA Violations
If data privacy and security is not adequately managed, HHS’ Office for Civil Rights can issue fines for non-compliance. Avoidable data breaches could see considerable financial penalties applied. Under the penalty structure brought in by HITECH Act and subsequently adjusted each year to account for inflation, violations can lead to fines up to a maximum of $2,134,831 per year for violations of an identical type. Lawsuits can also be initiated by state attorneys general and fines of up to $250,000 per violation category are possible. In some circumstances, Covered Entities and Business Associates may also be sued by victims of data breaches.
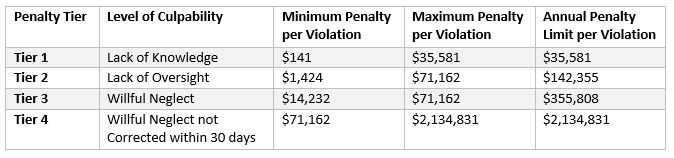
The penalty structure for 2025 is:
The high odds of healthcare organizations becoming targets for cybercriminals and the exorbitant cost of addressing data breaches – issuing breach notification correspondence, offering credit monitoring services and covering regulatory fines, and legal costs – is far higher than the cost of achieving full compliance. But, while the initial investment in the necessary technical, physical and administrative security measures to secure patient data may be high, the improvements can lead to savings over time as a result of improved efficiency. Organizations that have already implemented mechanisms to adhere with HIPAA often see their workflows streamlined and the workforce can become more productive, allowing healthcare organizations to reinvest their savings and provide a higher standard of healthcare to patients.
Explaining HIPAA to Staff
 Explaining HIPAA to staff may require more work than explaining HIPAA to patients. In order to comply with HIPAA, organizations must develop privacy and security policies for tall members of the workforce, and enforce a sanctions policy for staff who do not comply with the organization’s policies and procedures. Therefore it is important to explain HIPAA to workers HIPAA in greater detail.
Explaining HIPAA to staff may require more work than explaining HIPAA to patients. In order to comply with HIPAA, organizations must develop privacy and security policies for tall members of the workforce, and enforce a sanctions policy for staff who do not comply with the organization’s policies and procedures. Therefore it is important to explain HIPAA to workers HIPAA in greater detail.
The best method of explaining HIPAA to employees is in special compliance training tutorials. Although HIPAA does not require training to be provided other than when there is a material change to policies and procedures, there is so much for employees to take in relating to the security and privacy of personal health information, that compliance training sessions are better short and frequent. Trying to explain HIPAA to employees in a four-hour training session will likely fail.
A lot of the explanation will concentrate on the privacy and security of PHI, but how this is adopted will likely have an effect on the workforce. For instance, workforce members should be prevented from exchanging information about patient healthcare via personal mobile devices unless appropriate controls have been implemented. Due to the number of healthcare centers adopting BYOD policies, this will mean workers may have to download safe communication apps to their personal mobile devices in order to communicate ePHI.
HIPAA for Dummies: Summary
In a way, HIPAA was quite forward-thinking. Although Congress had been passing privacy laws since the 1970s, HIPAA addressed the digitalization of medical records and stipulated the safeguards HIPAA-covered entities should apply in order to protect healthcare data in both paper and digital formats. The digitalization of medical records was later encouraged via the introduction of the Meaningful Use incentive program in the HITECH Act 2009.
Compliance with HIPAA is an ongoing exercise. There is no one-off compliance test or certification one can achieve that will absolve a Covered Entity from sanctions if an avoidable breach or violation of HIPAA subsequently occurs. Indeed, OCR has issued a statement advising Covered Entities and Business Associates that it does not endorse any private consultants’ or education providers’ seminars, materials or systems, nor does it certify any persons or products as “HIPAA compliant.”
If you are unsure about any element of HIPAA, it is recommended you seek professional advice. It has already been mentioned above that ignorance of HIPAA is not an adequate excuse for noncompliance, and there does not necessarily need to have been an unauthorized disclosure of PHI in order for a violation of HIPAA to warrant sanctions. Therefore, although the resources required to achieve HIPAA compliance may be considerable, there is no alternative if your organization collects, processes, stores, or transmits PHI or ePHI than to become compliant with HIPAA.
HIPAA for Dummies FAQs
Are all disclosures of PHI without patient consent breaches of HIPAA?
Allowable disclosures of PHI include sharing PHI with the data subject (i.e. the patient), and when PHI is shared for treatment, payment, and health care operation activities. Exceptions to the disclosure rule also exist when a patient is incapacitated, when it is in the public interest for PHI to be disclosed, or when an unintended disclosure is “incident” to an allowable disclosure – i.e. if a patient´s age is disclosed when discussing his or her treatment options.
With regards to the HIPAA record retention requirements, is it okay to store records in the cloud?
HIPAA does not distinguish between retaining records in the cloud or on-premises; and in many circumstances it makes sense to take advantage of cloud services to reduce capital expenses in the IT department. However, before storing records in the cloud, it is necessary to sign a Business Associate Agreement with the Cloud Service Provider and have a full understanding of what areas of data security you are responsible for under the Provider´s “shared responsibility model”.
How do I know if I need to sign a Business Associate Agreement with a third party?
If a third party handles, uses, distributes, or accesses PHI during the provision of a services or the performance of a function or activity on behalf of a Covered Entity, they likely qualify as a Business Associate under HIPAA and it would be necessary to sign a Business Associate Agreement with them. It is also necessary to sign a Business Associate Agreement with any subcontractor that creates, receives, maintains, or transmits PHI on behalf of the Business Associate.
Why did it take seven years from the passage of HIPAA for the Privacy Rule to be enacted?
When HIPAA was passed in 1996, one of its clauses stated the Department for Health and Human Services (HHS) would only be responsible for developing privacy regulations if Congress did not enact privacy legislation within three years. HHS released its proposed HIPPA Privacy Rule in 1999; but, due to the volume of public comments (more than 52,000), the Final Rule was not published until 2002 with an effective date of April 2003.
Can a Covered Entity be held liable for a breach of HIPAA if an employee discloses PHI without authorization in their self-interest?
In certain circumstances – for example when the unauthorized disclosure is incidental to the employee´s normal duties – a Covered Entity can be held liable for a breach of HIPAA. The HHS´ Office of Civil Rights will take into account the efforts the Covered Entity has made to prevent unauthorized disclosures when calculating what penalties to impose; however, if the individual whose PHI has been illegally disclosed brings a civil action against the Covered Entity, a court may not take the same view.
The HIPAA Guide is a registered trademark. Copyright © 2007-2026 The HIPAA Guide. All rights reserved.